Bibliographie sur le consentement et la vie privée
~
- RGPD ~
- Droit ~
- Vie privée ~
- Utilisateurs
Une compilation d’articles, principalement académiques, sur le sujet du consentement dans le cadre du RGPD et du respect de la vie privée.
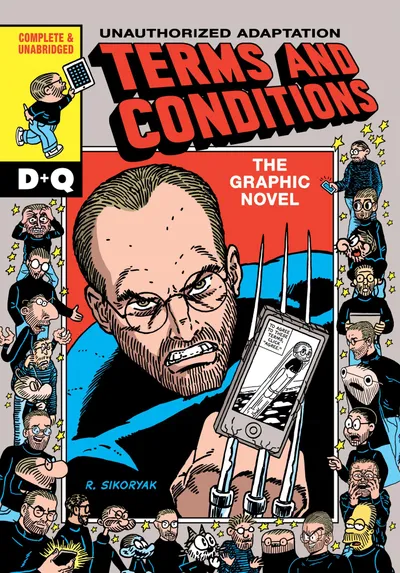
L’image de couverture est une vraie bande dessinée.
§︎ Ancre pour le titre : Généralités Généralités
- La forme des choix ➡️
Résumé
Le laboratoire d'innovation numérique de la CNIL (LINC) publie son 6ème cahier Innovation et prospective, La Forme des choix - Données personnelles, design et frictions désirables : une exploration des enjeux du design dans la conception des services numériques, au prisme de la protection des données et des libertés. - Privacy is a right to the appropriate flow of information. ➡️
Résumé
Privacy is a right to the appropriate flow of information. A third area where researchers may struggle is privacy. As Lowrance (2012) put it quite succinctly: “privacy should be respected because people should be respected.” Privacy, however, is a notoriously messy concept (Nissenbaum 2010, chap. 4), and, as such, it
§︎ Ancre pour le titre : Conception Conception
- No cookie for you ➡️
2020 ~
Résumé
Good news: we removed all cookie banners from GitHub! 🎉 No one likes cookie banners. But cookie banners are everywhere. So how did we pull this off? Well, EU law requires you to use cookie - Privacy transparency patterns ➡️
J. Siljee et al. ~ 2015 ~
Résumé
This paper describes two privacy patterns for creating privacy transparency: the Personal Data Table pattern and the Privacy Policy Icons pattern, as well as a full overview of privacy transparency patterns. It is a first step in creating a full set of privacy design patterns, which will aid software developers with the realization of privacy by design. Privacy design patterns are design solutions to recurring privacy problems; as such they can facilitate the development of privacy-by-design solutions. Privacy design patterns as such exist, but a complete, uniform and readily applicable overview does not exist. This paper presents such an overview for privacy transparency patterns: they focus on solutions on how to create privacy transparency. Two privacy transparency patterns are fully described: the Personal Data Table pattern and the Privacy Policy Icons pattern. - Smashing Magazine Privacy UX: Better Cookie Consent Experiences ➡️
Résumé
In this second part of the series, we’ll look into notorious GDPR cookie consent prompts, and how we can design the experience around them better — with our users’ privacy in mind, of course. - Designing Friction For A Better User Experience ➡️
Résumé
In experience design, friction is usually the opposite of being intuitive or effortless. However, that doesn’t mean that it’s always bad for the users. In this article, you’ll learn when and how friction can be an efficient tool to actually design better experiences. - Report: Deceived by design ➡️
Résumé
How tech companies use dark patterns to discourage us from exercising our rights to privacy. - Dark Patterns.org ➡️
Résumé
Dark Patterns are tricks used in websites and apps that make you buy or sign up for things that you didn't mean to. The purpose of this site is to spread awareness and to shame companies that use them. - Gauthier Roussilhe | A fundamental critique of seamless design ➡️
- How gambling apps are facilitating dangerous addiction ➡️
Résumé
Our constant proximity to technology is making gambling addiction much more common - Designing a product with mental health issues in mind ➡️
Résumé
How we're designing Monzo to be a powerful and unique financial service for our most vulnerable customers. - Legal Design Patterns For Privacy ➡️
PDF ~
§︎ Ancre pour le titre : Visualisation Visualisation
- Picture superiority effect ➡️
2020 ~
Résumé
The picture superiority effect refers to the phenomenon in which pictures and images are more likely to be remembered than words. This effect has been demonstrated in numerous experiments using different methods. It is based on the notion that "human memory is extremely sensitive to the symbolic modality of presentation of event information". Explanations for the picture superiority effect are not concrete and are still being debated. - Privacy Icons: A Risk-Based Approach to Visualisation of Data Processing ➡️
Z. Efroni et al. ~ 2019 ~
- Disconnect: Privacy Icons ➡️
- Towards a Visual Vocabulary for Privacy Concepts ➡️
V. Motti et al. ~ 2016 ~
Résumé
Designing privacy controls that are intuitive for end users involves several challenges. Graphic representations could certainly contribute to tackle such challenges, however, a visual vocabulary for privacy solutions is currently lacking. To contribute to that end, in this paper we report a review of online images related to privacy. We identify graphic representations that illustrate privacy objects, mechanisms and actions, and categorize them according to the concepts covered. Seeking to develop a set of icons to illustrate privacy concepts, we analyze online contents publicly available from social media and extract representations that commonly refer to privacy concepts. The contributions of this paper include: (1) a set of graphics that represent privacy mechanisms, objects and actions; and (2) a vocabulary for such graphic representation. The evidence is drawn from the analysis and discussion of 241 images selected by the authors from ten online image repositories. - Standardizing privacy notices: an online study of the nutrition label approach ➡️
P. Kelley et al. ~ 2010 ~
Résumé
Earlier work has shown that consumers cannot effectively find information in privacy policies and that they do not enjoy using them. In our previous research we developed a standardized table format for privacy policies. We compared this standardized format, and two short variants (one tabular, one text) with the current status quo: full text natural-language policies and layered policies. We conducted an online user study of 764 participants to test if these three more-intentionally designed, standardized privacy policy formats, assisted by consumer education, can benefit consumers. Our results show that standardized privacy policy presentations can have significant positive effects on accuracy and speed of information finding and on reader enjoyment of privacy policies. - A "nutrition label" for privacy ➡️
P. Kelley et al. ~ 2009 ~ PDF ~
Résumé
We used an iterative design process to develop a privacy label that presents to consumers the ways organizations collect, use, and share personal information. Many surveys have shown that consumers are concerned about online privacy, yet current mechanisms to present website privacy policies have not been successful. This research addresses the present gap in the communication and understanding of privacy policies, by creating an information design that improves the visual presentation and comprehensibility of privacy policies. Drawing from nutrition, warning, and energy labeling, as well as from the effort towards creating a standardized banking privacy notification, we present our process for constructing and refining a label tuned to privacy. This paper describes our design methodology; findings from two focus groups; and accuracy, timing, and likeability results from a laboratory study with 24 participants. Our study results demonstrate that compared to existing natural language privacy policies, the proposed privacy label allows participants to find information more quickly and accurately, and provides a more enjoyable information seeking experience. - Iconset für Datenschutzerklärungen ➡️
. wetter et al. ~
Résumé
Datenschutzerklärungen sind meist langatmige Texte, deren Kernaussagen sich nicht unbedingt leicht erschließen lassen. Webdienste werden international genutzt. Persönliche Daten werden in immer komplexeren Strukturen gespeichert und verarbeitet. Aber wer liest schon die Datenschutzerklärung, geschwe - Appropriate Privacy Icons ➡️
Résumé
Privacy design patterns for software engineering - Privacy Dashboard ➡️
Résumé
Built for Mobile from The Ground Up ACT | The App Association has developed the Privacy Dashboard, an open source privacy policy display optimized for the small screens of smartphones and tablets. With a graphical interface familiar to mobile device users, the Privacy Dashboard provides a simple way for consumers to review - Privacy Tool Lets Users Quickly Rank Websites on Privacy Policies ➡️
Résumé
A new tool and web site launched today purports to clear some of the fog around the issue of online privacy. PrivacyChoice has analyzed more than a thousand of the most trafficked web sites to score them on a scale of 1 to 100 in their collection and use of personal data, as well as the collection and use practices of the third-party companies that they allow to track users on their sites. - Privacy Icons - MozillaWiki ➡️
- The Use of Privacy Icons and Standard Contract Terms for Generating Consumer Trust and Confidence in Digital Services ➡️
§︎ Ancre pour le titre : Théorie Théorie
- The Myth of the Privacy Paradox ➡️
D. Solove et al. ~ 2020 ~
Résumé
In this article, Professor Daniel Solove deconstructs and critiques the privacy paradox and the arguments made about it. The “privacy paradox” is the phenomenon where people say that they value privacy highly, yet in their behavior relinquish their personal data for very little in exchange or fail to use measures to protect their privacy. Commentators typically make one of two types of arguments about the privacy paradox. On one side, the “behavior valuation argument” contends behavior is the best metric to evaluate how people actually value privacy. Behavior reveals that people ascribe a low value to privacy or readily trade it away for goods or services. The argument often goes on to contend that privacy regulation should be reduced. On the other side, the “behavior distortion argument” argues that people’s behavior isn’t an accurate metric of preferences because behavior is distorted by biases and heuristics, manipulation and skewing, and other factors. In contrast to both of these camps, Professor Solove argues that the privacy paradox is a myth created by faulty logic. The behavior involved in privacy paradox studies involves people making decisions about risk in very specific contexts. In contrast, people’s attitudes about their privacy concerns or how much they value privacy are much more general in nature. It is a leap in logic to generalize from people’s risk decisions involving specific personal data in specific contexts to reach broader conclusions about how people value their own privacy. The behavior in the privacy paradox studies doesn’t lead to a conclusion for less regulation. On the other hand, minimizing behavioral distortion will not cure people’s failure to protect their own privacy. It is perfectly rational for people — even without any undue influences on behavior — to fail to make good assessments of privacy risks and to fail to manage their privacy effectively. Managing one’s privacy is a vast, complex, and never-ending project that does not scale; it becomes virtually impossible to do comprehensively. Privacy regulation often seeks to give people more privacy self-management, such as the recent California Consumer Privacy Act. Professor Solove argues that giving individuals more tasks for managing their privacy will not provide effective privacy protection. Instead, regulation should employ a different strategy — focus on regulating the architecture that structures the way information is used, maintained, and transferred. - The Pathologies of Digital Consent ➡️
N. Richards et al. ~ 2019 ~
Résumé
Consent permeates both our law and our lives — especially in the digital context. Consent is the foundation of the relationships we have with search engines, social networks, commercial web sites, and any one of the dozens of other digitally mediated businesses we interact with regularly. We are frequently asked to consent to terms of service, privacy notices, the use of cookies, and so many other commercial practices. Consent is important, but it’s possible to have too much of a good thing. As a number of scholars have documented, while consent models permeate the digital consumer landscape, the practical conditions of these agreements fall far short of the gold standard of knowing and voluntary consent. Yet as scholars, advocates, and consumers, we lack a common vocabulary for talking about the different ways in which digital consents can be flawed.This article offers four contributions to improve our understanding of consent in the digital world. First, we offer a conceptual vocabulary of “the pathologies of consent” — a framework for talking about different kinds of defects that consent models can suffer, such as unwitting consent, coerced consent, and incapacitated consent. Second, we offer three conditions for when consent will be most valid in the digital context: when choice is infrequent, when the potential harms resulting from that choice are vivid and easy to imagine, and where we have the correct incentives choose consciously and seriously. The further we fall from these conditions, the more a particular consent will be pathological and thus suspect. Third, we argue that out theory of consent pathologies sheds light on the so-called “privacy paradox” — the notion that there is a gap between what consumers say about wanting privacy and what they actually do in practice. Understanding the “privacy paradox” in terms of consent pathologies shows how consumers are not hypocrites who say one thing but do another. On the contrary, the pathologies of consent reveal how consumers can be nudged and manipulated by powerful companies against their actual interests, and that this process is easier when consumer protection law falls far from the gold standard. In light of these findings, we offer a fourth contribution — the theory of consumer trust we have suggested in prior work and which we further elaborate here as an alternative to our over-reliance on consent and its many pathologies. - A Design Space for Effective Privacy Notices ➡️
- Privacy as Trust: Sharing Personal Information in a Networked World ➡️
A. Waldman et al. ~ 2014 ~
Résumé
This Article is the first in a series on the legal and sociological aspects of privacy, arguing that private contexts are defined by relationships of trust among individuals. The argument reorients privacy scholarship from an individual right to social relationships of disclosure. This has implications for a wide variety of vexing problems of modern privacy law, from limited disclosures to “revenge porn.” The common everyday understanding is that privacy is about choice, autonomy, and individual freedom. It encompasses the individual’s right to determine what he will keep hidden and what, how, and when he will disclose to the public. Privacy is his respite from the prying, conformist eyes of the rest of the world and his expectation that the things about himself that he wants to keep private will remain so. These ways of understanding privacy are variations on the same theme: that privacy is a tool of the individual “against the world.” None of them adequately protect personal privacy where sharing personal information with others is a precondition of modern life. This Article argues that privacy is really about trust. Rather than accept the traditional division between public and private, and rather than begin and end the discussion of privacy as an individual right, this Article bridges social science and the law to argue that disclosures in contexts of trust are private. Trusting relationships are determined by the presence of experience, strong overlapping networks, identity sharing, and other indicia derived from the totality of the circumstances. This conceptualization of privacy, and its related ways of defining when invasions of privacy occur, more effectively protects privacy in a modern digital world. - Choosing Not to Choose ➡️
C. Sunstein et al. ~ 2014 ~
Résumé
Choice can be an extraordinary benefit or an immense burden. In some contexts, people choose not to choose, or would do so if they were asked. For example, many people prefer not to make choices about their health or retirement plans; they want to delegate those choices to a private or public institution that they trust (and may well be willing to pay a considerable amount for such delegations). This point suggests that however well-accepted, the line between active choosing and paternalism is often illusory. When private or public institutions override people’s desire not to choose, and insist on active choosing, they may well be behaving paternalistically, through a form of choice-requiring paternalism. Active choosing can be seen as a form of libertarian paternalism, and a frequently attractive one, if people are permitted to opt out of choosing in favor of a default (and in that sense not to choose); it is a form of nonlibertarian paternalism insofar as people are required to choose. For both ordinary people and private or public institutions, the ultimate judgment in favor of active choosing, or in favor of choosing not to choose, depends largely on the costs of decisions and the costs of errors. But the value of learning, and of developing one’s own preferences and values, is also important, and may argue on behalf of active choosing, and against the choice not to choose. For law and policy, these points raise intriguing puzzles about the idea of “predictive shopping,” which is increasingly feasible with the rise of large data sets containing information about people’s previous choices. Some empirical results are presented about people’s reactions to predictive shopping; the central message is that most (but not all) people reject predictive shopping in favor of active choosing. - Notice and consent in a world of Big Data ➡️
F. Cate et al. ~ 2013 ~
Résumé
Nowadays individuals are often presented with long and complex privacy notices routinely written by lawyers for lawyers, and are then requested to either ‘consent’ or abandon the use of the desired service.The over-use of notice and consent presents increasing challenges in an age of ‘Big Data’.These phenomena are receiving attention particularly in the context of the current review of the OECD Privacy Guidelines.In 2012 Microsoft sponsored an initiative designed to engage leading regulators, industry executives, public interest advocates, and academic experts in frank discussions about the role of individual control and notice and consent in data protection today, and alternative models for providing better protection for both information privacy and valuable data flows in the emerging world of Big Data and cloud computing. - On Notice: The Trouble with Notice and Consent ➡️
S. Barocas et al. ~ 2009 ~
Résumé
This paper scrutinizes the use of ‘notice and consent’ to address privacy concerns in online behavioral advertising (OBA). It is part of a larger project with Dan Boneh, Arvind Narayanan, and Vincent Toubiana to evaluate the social, political, and ethical standing of OBA and to develop a system (PRIVADS) for privacy- preserving OBA. We develop a distinction between the ethical implications of the (1) tracking that is required to develop user profiles to be used in the (2) targeting of individual users with particular ads. We show how tracking and targeting present both distinct and overlapping ethical concerns and how existing mitigations tend to treat these concerns as one and the same, even when they seem to address different problems. Anonymization, for instance, attempts to defuse the privacy concerns of tracking by excluding ‘personally identifiable’ or ‘sensitive’ information, but offers little to quell concerns over targeting. On the other hand, policy solutions, particularly notice and consent, attempt to render participation a matter of choice, but generally fail to explain whether a user agrees or disagrees to tracking, targeting, or both. Moreover, we show how various types of complexity render current notice mechanisms practically and inherently insufficient. This is due to (1) the confusing disconnect between the privacy policies of online publishers and the tracking and targeting third parties with whom they contract, each of whom have their own privacy policies; (2) the fickle nature of privacy policies, which may change at any time, often with short notice, and (3) the ever-increasing number of players in the ad network and exchange space, resulting in flows of user data that are opaque to users. To the extent that meaningful notice remains illusory under such conditions, we conclude that even an opt-in regime would lack legitimacy. - Beyond informed consent ➡️
Z. Bhutta et al. ~ 2004 ~ PDF ~
Résumé
Although a relatively recent phenomenon, the role of informed consent in human research is central to its ethical regulation and conduct. However, guidelines often recommend procedures for obtaining informed consent (usually written consent) that are difficult to implement in developing countries. This paper reviews the guidelines for obtaining informed consent and also discusses prevailing views on current controversies, ambiguities and problems with these guidelines and suggests potential solutions. The emphasis in most externally sponsored research projects in developing countries is on laborious documentation of several mechanical aspects of the research process rather than on assuring true comprehension and voluntary participation. The onus for the oversight of this process is often left to overworked and ill-equipped local ethics review committees. Current guidelines and processes for obtaining informed consent should be reviewed with the specific aim of developing culturally appropriate methods of sharing information about the research project and obtaining and documenting consent that is truly informed. Further research is needed to examine the validity and user friendliness of innovations in information sharing procedures for obtaining consent in different cultural settings.
§︎ Ancre pour le titre : Études statistiques, psycho et comportementales Études statistiques, psycho et comportementales
- Hyperbolic discounting ➡️
2020 ~
Résumé
In economics, hyperbolic discounting is a time-inconsistent model of delay discounting. It is one of the cornerstones of behavioral economics and its brain-basis is actively being studied by neuroeconomics researchers.The discounted utility approach states that intertemporal choices are no different from other choices, except that some consequences are delayed and hence must be anticipated and discounted (i.e., reweighted to take into account the delay). Given two similar rewards, humans show a preference for one that arrives sooner rather than later. Humans are said to discount the value of the later reward, by a factor that increases with the length of the delay. In the financial world, this process is normally modeled in the form of exponential discounting, a time-consistent model of discounting. Many psychological studies have since demonstrated deviations in instinctive preference from the constant discount rate assumed in exponential discounting. Hyperbolic discounting is an alternative mathematical model that agrees more closely with these findings.According to hyperbolic discounting, valuations fall relatively rapidly for earlier delay periods (as in, from now to one week), but then fall more slowly for longer delay periods (for instance, more than a few days). For example, in an early study subjects said they would be indifferent between receiving $15 immediately or $30 after 3 months, $60 after 1 year, or $100 after 3 years. These indifferences reflect annual discount rates that declined from 277% to 139% to 63% as delays got longer. This contrasts with exponential discounting, in which valuation falls by a constant factor per unit delay and the discount rate stays the same. The standard experiment used to reveal a test subject's hyperbolic discounting curve is to compare short-term preferences with long-term preferences. For instance: "Would you prefer a dollar today or three dollars tomorrow?" or "Would you prefer a dollar in one year or three dollars in one year and one day?" It has been claimed that a significant fraction of subjects will take the lesser amount today, but will gladly wait one extra day in a year in order to receive the higher amount instead. Individuals with such preferences are described as "present-biased". The most important consequence of hyperbolic discounting is that it creates temporary preferences for small rewards that occur sooner over larger, later ones. Individuals using hyperbolic discounting reveal a strong tendency to make choices that are inconsistent over time – they make choices today that their future self would prefer not to have made, despite knowing the same information. This dynamic inconsistency happens because hyperbolas distort the relative value of options with a fixed difference in delays in proportion to how far the choice-maker is from those options. - Only 9% of visitors give GDPR consent to be tracked ➡️
M. Saric et al. ~
Résumé
Privacy regulations such as the GDPR say that you need to seek permission from your website visitors before tracking them. - Baromètre 2020 RGPD & Cookies : les premiers chiffres ➡️
L. Cherpin et al. ~ 2020 ~ PDF ~
Résumé
Découvrez les premiers chiffres de notre Baromètre 2020 RGPD & Cookies et inscrivez-vous sur notre site pour recevoir le baromètre complet. - Situational user consent for access to personal Information: Does purpose make any difference? ➡️
N. Steinfeld et al. ~ 2020 ~
Résumé
Privacy literature in recent years has emphasized the role of context and situation in individuals' privacy regulation. While most research is focused on understanding situational effects on self-disclosure, the role of situational factors in users’ decision to consent for third-party access to information, a common practice with significant privacy implications, has been barely investigated. The current study bridges this gap by adopting the framework of situational privacy to examine the effect of the purpose for information collection on participants' consent. An online experiment examined users' consent to allow access to their Facebook profile to an unknown entity, with requests distinguished by the framing of the purpose for collecting information as related to security, commercial or academic research. Contrary to the study’s hypothesis, consent rate was similar between groups and purpose was non-significant in explaining participants’ decisions. Furthermore, in all three groups- compensation amount and general willingness to disclose information explain user consent, regardless of purpose. However, some specific factors significantly correlate with consent in each group separately. The study concludes that due to blurring boundaries and uncertainties regarding real uses of information, when it comes to consent for third-party access, predetermined attitudes and preferences are main factors influencing users’ decisions, thus a situational framework is partly adequate for explaining variations in user consent decisions. - Dark Patterns after the GDPR: Scraping Consent Pop-ups and Demonstrating their Influence ➡️
M. Nouwens et al. ~ 2020 ~ PDF ~
Résumé
New consent management platforms (CMPs) have been introduced to the web to conform with the EU’s General Data Protection Regulation, particularly its requirements for consent when companies collect and process users’ personal data. This work analyses how the most prevalent CMP designs affect people’s consent choices. We scraped the designs of the five most popular CMPs on the top 10,000 websites in the UK (n=680). We found that dark patterns and implied consent are ubiquitous; only 11.8% meet the minimal requirements that we set based on European law. Second, we conducted a field experiment with 40 participants to investigate how the eight most common designs affect consent choices. We found that notification style (banner or barrier) has no effect; removing the opt-out button from the first page increases consent by 22–23 percentage points; and providing more granular controls on the first page decreases consent by 8–20 percentage points. This study provides an empirical basis for the necessary regulatory action to enforce the GDPR, in particular the possibility of focusing on the centralised, third-party CMP services as an effective way to increase compliance. - Multiple Purposes, Multiple Problems: A User Study of Consent Dialogs after GDPR ➡️
D. Machuletz et al. ~ 2020 ~ PDF ~
Résumé
The European Union's General Data Protection Regulation (GDPR) requires websites to ask for consent to the use of cookies for \emph{specific purposes}. This enlarges the relevant design space for consent dialogs. Websites could try to maximize click-through rates and positive consent decision, even at the risk of users agreeing to more purposes than intended. We evaluate a practice observed on popular websites by conducting an experiment with one control and two treatment groups ($N=150$ university students in two countries). We hypothesize that users' consent decision is influenced by (1) the number of options, connecting to the theory of choice proliferation, and (2) the presence of a highlighted default button ("select all''), connecting to theories of social norms and deception in consumer research. The results show that participants who see a default button accept cookies for more purposes than the control group, while being less able to correctly recall their choice. After being reminded of their choice, they regret it more often and perceive the consent dialog as more deceptive than the control group. Whether users are presented one or three purposes has no significant effect on their decisions and perceptions. We discuss the results and outline policy implications. - The ICO’s Cookie Consent Rate Dropped 90 Percent After Implementing its Own Best Practices ➡️
2019 ~
Résumé
We’ve seen quite a range of interpretations from digital publishers of how consumer consent for data processing should be collected under the EU’s general data protection regulation (GDPR) which […] - (Un)informed Consent: Studying GDPR Consent Notices in the Field ➡️
C. Utz et al. ~ 2019 ~ PDF ~
Résumé
Since the adoption of the General Data Protection Regulation (GDPR) in May 2018 more than 60 % of popular websites in Europe display cookie consent notices to their visitors. This has quickly led to users becoming fatigued with privacy notifications and contributed to the rise of both browser extensions that block these banners and demands for a solution that bundles consent across multiple websites or in the browser. In this work, we identify common properties of the graphical user interface of consent notices and conduct three experiments with more than 80,000 unique users on a German website to investigate the influence of notice position, type of choice, and content framing on consent. We find that users are more likely to interact with a notice shown in the lower (left) part of the screen. Given a binary choice, more users are willing to accept tracking compared to mechanisms that require them to allow cookie use for each category or company individually. We also show that the wide-spread practice of nudging has a large effect on the choices users make. Our experiments show that seemingly small implementation decisions can substantially impact whether and how people interact with consent notices. Our findings demonstrate the importance for regulation to not just require consent, but also provide clear requirements or guidance for how this consent has to be obtained in order to ensure that users can make free and informed choices. - Does the GDPR Enhance Consumers’ Control over Personal Data? An Analysis from a Behavioural Perspective ➡️
I. van Ooijen et al. ~ 2019 ~ PDF ~
Résumé
Because of increased technological complexities and multiple data-exploiting business practices, it is hard for consumers to gain control over their own personal data. Therefore, individual control over personal data has become an important subject in European privacy law. Compared to its predecessor, the General Data Protection Regulation (GDPR) addresses the need for more individual control over personal data more explicitly. With the introduction of several new principles that seem to empower individuals in gaining more control over their data, its changes relative to its predecessors are substantial. It appears, however, that, to increase individual control, data protection law relies on certain assumptions about human decision making. In this work, we challenge these assumptions and describe the actual mechanisms of human decision making in a personal data context. Further, we analyse the extent to which new provisions in the GDPR effectively enhance individual control through a behavioural lens. To guide our analysis, we identify three stages of data processing in the data economy: (1) the information receiving stage, (2) the approval and primary use stage, and (3) the secondary use (reuse) stage. For each stage, we identify the pitfalls of human decision-making that typically emerge and form a threat to individual control. Further, we discuss how the GDPR addresses these threats by means of several legal provisions. Finally, keeping in mind the pitfalls in human decision-making, we assess how effective the new legal provisions are in enhancing individual control. We end by concluding that these legal instruments seem to have made a step towards more individual control, but some threats to individual control remain entrenched in the GDPR. - Gambling on Smartphones: A Study of a Potentially Addictive Behaviour in a Naturalistic Setting ➡️
R. James et al. ~ 2019 ~
Résumé
Smartphone users engage extensively with their devices, on an intermittent basis for short periods of time. These patterns of behaviour have the potential to make mobile gambling especially perseverative. This paper reports the first empirical study of mobile gambling in which a simulated gambling app was used to measure gambling behaviour in phases of acquisition and extinction. We found that participants showed considerable perseverance in the face of continued losses that were linearly related to their prior engagement with the app. Latencies between gambles were associated with the magnitude of reinforcement; more positive outcomes were associated with longer breaks between play and a greater propensity to end a gambling session. Greater latencies were associated with measurements of problem gambling, and perseverance with gambling-related cognitions and sensation-seeking behaviour. - Networked privacy: How teenagers negotiate context in social media ➡️
A. Marwick et al. ~ 2014 ~
Résumé
While much attention is given to young people’s online privacy practices on sites like Facebook, current theories of privacy fail to account for the ways in which social media alter practices of information-sharing and visibility. Traditional models of privacy are individualistic, but the realities of privacy reflect the location of individuals in contexts and networks. The affordances of social technologies, which enable people to share information about others, further preclude individual control over privacy. Despite this, social media technologies primarily follow technical models of privacy that presume individual information control. We argue that the dynamics of sites like Facebook have forced teens to alter their conceptions of privacy to account for the networked nature of social media. Drawing on their practices and experiences, we offer a model of networked privacy to explain how privacy is achieved in networked publics. - L’UX est dynamique ! Comprendre la temporalité de l’UX ➡️
2014 ~
Résumé
Vous connaissez les 3 facteurs classiques de l’UX que sont le système, l’utilisateur et le contexte ? Ajoutez dès aujourd’hui la temporalité à votre liste de priorités ! En effet, s’il est possible… - Choice without Awareness: Ethical and Policy Implications of Defaults ➡️
N. Smith et al. ~ 2013 ~
Résumé
Defaults have such powerful and pervasive effects on consumer behavior that they could be considered “hidden persuaders” in some settings. Ignoring defaults is not a sound option for marketers or consumer policy makers. The authors identify three theoretical causes of default effects—implied endorsement, cognitive biases, and effort—to guide thought on the appropriate marketer and policy maker responses to the issues posed for consumer welfare and consumer autonomy, including proposals for benign “nudges” of behavior. Defaults can be a preferred form of decision architecture; that is, other nonconscious influences on choice and an absence of established preferences can mean that active choice is not always the better alternative. The authors propose “smart defaults” as welfare-enhancing and market-oriented alternatives to the current practice of generally ignoring default effects. Their analysis highlights the importance of considering the process as well as the outcomes of consumer decision making and taking responsibility for consumers' mistakes arising from misuse of defaults. The authors conclude by reflecting on the ethical and policy implications of techniques that influence consumer choice without awareness. - Consent for all: revealing the hidden complexity of terms and conditions ➡️
E. Luger et al. ~ 2013 ~
Résumé
Terms and conditions are central in acquiring user consent by service providers. Such documents are frequently highly complex and unreadable, placing doubts on the validity of so called 'informed consent'. While readability and web accessibility have been major themes for some time in HCI, the core principles have yet to be applied beyond webpage content and are absent from the underpinning terms and conditions. Our concern is that accessible web pages will encourage consent, masking the complexities of the terms of usage. Using the SMOG readability formula and UK Energy services as a case study, we observed that a series of supplier terms and conditions were far beyond what a functionally literate adult could be expected to understand. We also present a browser based plug-in which compares SMOG readability scores to popular books. The intention is to use this plug-in to assist in surfacing the hidden complexities underpinning online consent. - Why Johnny can't opt out: a usability evaluation of tools to limit online behavioral advertising ➡️
P. Leon et al. ~ 2012 ~
Résumé
We present results of a 45-participant laboratory study investigating the usability of nine tools to limit online behavioral advertising (OBA). We interviewed participants about OBA and recorded their behavior and attitudes as they configured and used a privacy tool, such as a browser plugin that blocks requests to specific URLs, a tool that sets browser cookies indicating a user's preference to opt out of OBA, or the privacy settings built into a web browser. We found serious usability flaws in all tools we tested. Participants found many tools difficult to configure, and tools' default settings were often minimally protective. Ineffective communication, confusing interfaces, and a lack of feedback led many participants to conclude that a tool was blocking OBA when they had not properly configured it to do so. Without being familiar with many advertising companies and tracking technologies, it was difficult for participants to use the tools effectively. - "What did I just sign?": On informed consent in China ➡️
2009 ~
Résumé
My husband John had done everything the Human Subjects Committee asked. He reviewed the study with his departmental ethics representative, completed - Recommendations Implicit in Policy Defaults ➡️
C. McKenzie et al. ~ 2006 ~
Résumé
Should people be considered organ donors after their death unless they request not to be, or should they not be considered donors unless they request to be? Because people tend to stay with the default in a variety of domains, policymakers' choice of default has large and often important effects. In the United States, where the organ-donation policy default is “not a donor,” about 5,000 people die every year because there are too few donors. Four experiments examined two domains—being an organ donor and saving for retirement—where default effects occur and have important implications. The results indicate that default effects occur in part because policymakers' attitudes can be revealed through their choice of default, and people perceive the default as indicating the recommended course of action. Policymakers need to be aware of the implicit messages conveyed by their choice of default. - Evocation of freedom and compliance: the but you are free of… technique ➡️
N. Guéguen et al. ~ 2000 ~ PDF ~
Résumé
Many investigations showed that the semantic characteristics of a request could lead to more compliance. A feeling of freedom is also a factor favoring compliance to numerous types of requests. An experiment was carried out, in which the evocation of freedom was formulated verbally, following a demand for money made by confederates. Results show that the verbal incentive used (demand for money + "but you are free to accept or to refuse") increased the rate of subjects’ compliance as well as the average amount of granted gifts. The semantic activation of the feeling of freedom is discussed within the framework of numerous paradigms of research on compliance. - The unbearable lightness of user consent ➡️
- Over 90% of users consent to GDPR requests says Quantcast after enabling 1bn of them ➡️
Résumé
Over the past two months, 90% of consumers have consented to GDPR requests from publishers and marketers, according to adtech outfit Quantcast which has processed 1bn of them. - Risk Reduction Strategies on Facebook ➡️
- Dark Patterns at Scale: Findings from a Crawl of 11K Shopping Websites ➡️
§︎ Ancre pour le titre : Divers Divers
- Should I Agree? Delegating Consent Decisions Beyond the Individual ➡️
B. Nissen et al. ~ 2019 ~ PDF ~
Résumé
Obtaining meaningful user consent is increasingly problematic in a world of numerous, heterogeneous digital services. Current approaches (e.g. agreeing to Terms and Conditions) are rooted in the idea of individual control despite growing evidence that users do not (or cannot) exercise such control in informed ways. We consider an alternative approach whereby users can opt to delegate consent decisions to an ecosystem of third-parties including friends, experts, groups and AI entities. We present the results of a study that used a technology probe at a large festival to explore initial public responses to this reframing -- focusing on when and to whom users would delegate such decisions. The results reveal substantial public interest in delegating consent and identify differing preferences depending on the privacy context, highlighting the need for alternative decision mechanisms beyond the current focus on individual choice. - Against Notice Skepticism in Privacy (and Elsewhere) ➡️
M. Calo et al. ~ 2012 ~
- ToS;DR - Terms of Service; Didn't Read ➡️